The importance of cybersecurity in facilitating productive remote work was a significant catalyst for the two years-worth of digital transformation we observed in the first two months of the COVID-19 pandemic. In this era of ubiquitous computing, security solutions don’t just sniff out threats, they serve as control planes for improving productivity and collaboration by giving end-users easier access to more corporate resources. Microsoft recently concluded a survey of nearly 800 business leaders of companies of more than 500 employees in India (IN), Germany (DE), the United Kingdom (UK) and the United States (US) to better understand their views of the pandemic threat landscape, implications for budgets and staffing, and how they feel the pandemic could reshape the cyber-security long-term.
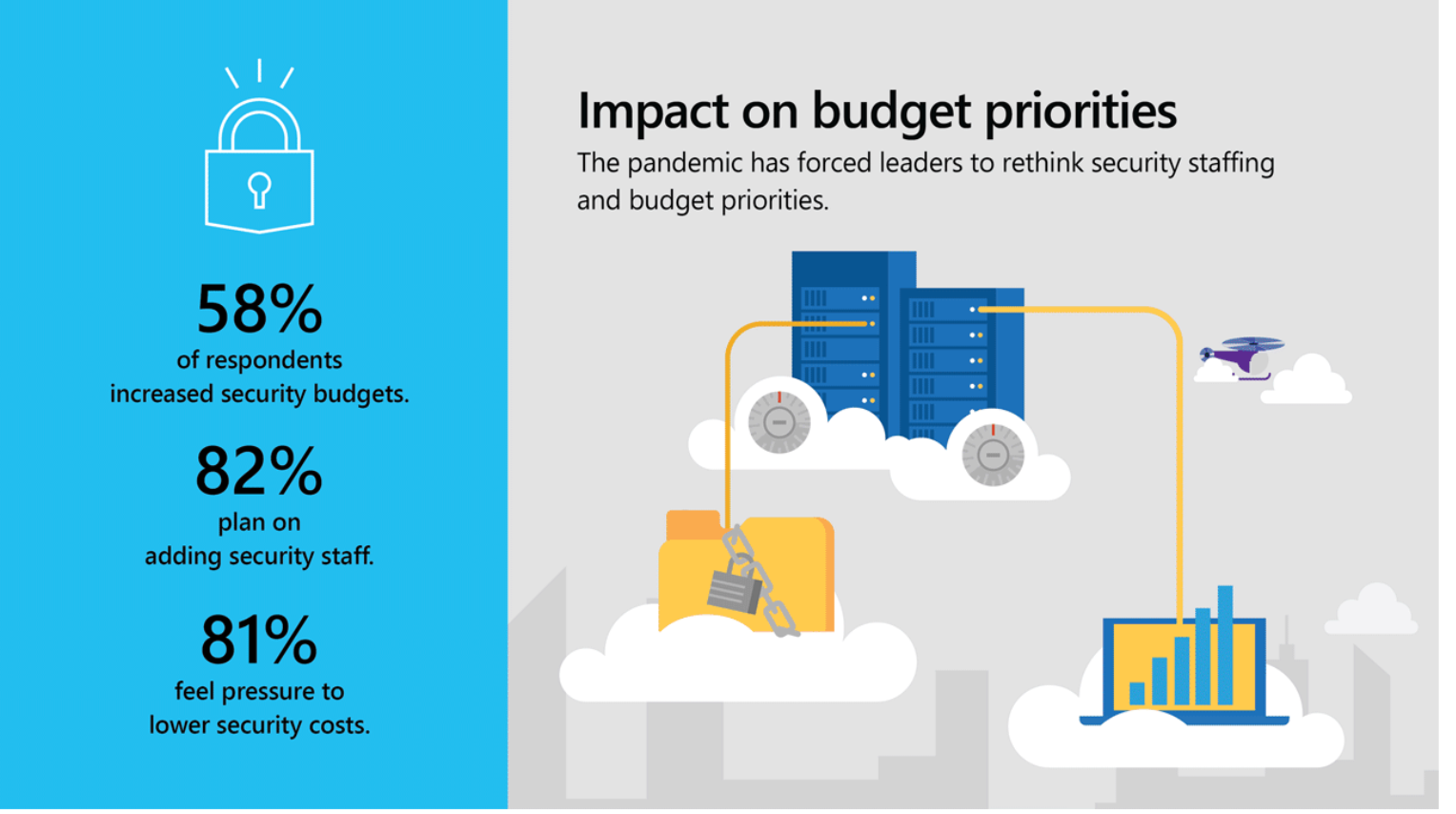
Among the key insights are data showing that an alarming number of businesses are still impacted by phishing scams, security budgets, and hiring increased in response to COVID-19, and cloud-based technologies and architectures like Zero Trust are significant areas of investment moving forward.
Improving Productivity & Mitigating Threats
Security and IT teams have been working overtime to meet business goals while simultaneously staying ahead of new threats and scams. “Providing secure remote access to resources, apps, and data” is the #1 challenge reported by security leaders. For many businesses, the limits of the trust model they had been using, which leaned heavily on company-managed devices, physical access to buildings, and limited remote access to select line-of-business apps, got exposed early on in the pandemic. This paradigm shift has been most acute in the limitations of basic username/password authentication. As a result, when asked to identify the top security investment made during the pandemic the top response was Multi-factor authentication (MFA).